What happened
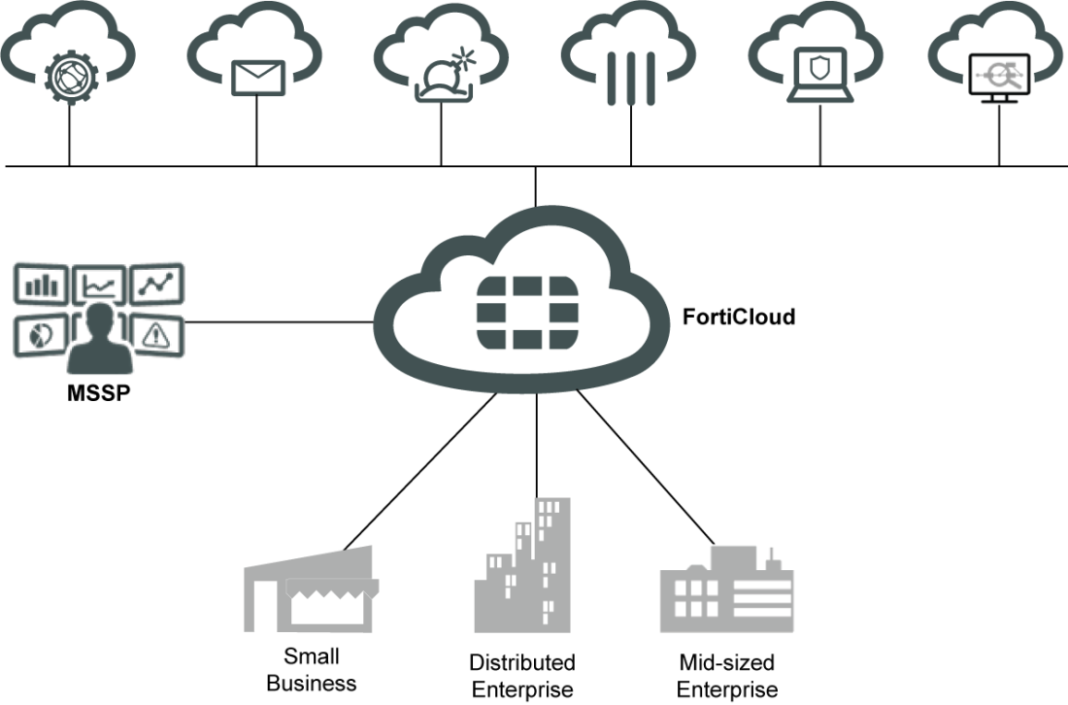
An authentication bypass vulnerability affecting FortiCloud Single Sign-On was confirmed to be actively exploited. The flaw allows attackers with a FortiCloud account to authenticate to unrelated Fortinet devices when SSO is enabled. The vulnerability was added to the Known Exploited Vulnerabilities catalog.
Who is affected
Fortinet devices with FortiCloud SSO enabled are directly exposed to exploitation.
Why CISOs should care
Authentication bypass vulnerabilities undermine administrative access controls across network security infrastructure.
3 practical actions
- Inventory FortiCloud SSO usage. Identify enabled systems.
- Apply available patches. Update affected products.
- Review authentication logs. Monitor for anomalous access activity.