Lately, the Cybersecurity and Infrastructure Security Agency (CISA) has been buried under troubling headlines. Steep workforce reductions. $700 million 2027 budget cut. Leadership uncertainty. Impacts from the months-long partial government shutdown. Canceled 2026 CyberCorps: Scholarship for Service program.
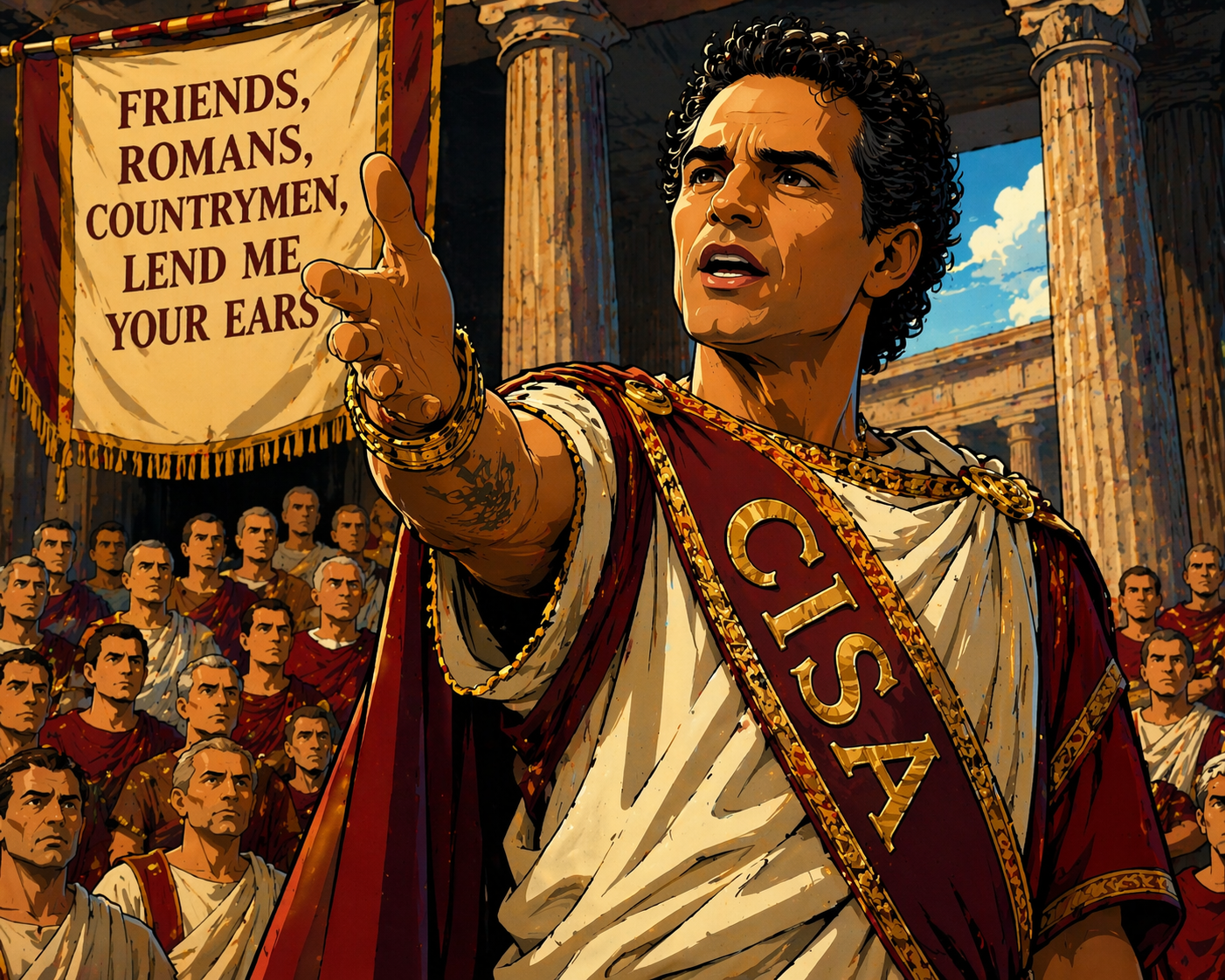
But, to borrow and twist a phrase from Shakespeare’s Julius Caesar, “I come to praise CISA, not bury it.”
CISA and I grew up together in the federal cyber space.
I assumed the CISO role at the US Department of Labor in August 2018, just a few months before CISA was established in November 2018, when President Trump signed the Cybersecurity and Infrastructure Security Agency Act, elevating the National Protection and Programs Directorate (NPPD) into a standalone agency within DHS.
Throughout my tenure at DOL (I resigned from federal service in April 2025) CISA was a valuable and trusted partner. The services CISA provided to agencies helped us defend against, detect, and respond to cybersecurity threats – preventing or minimizing immeasurable instances of sensitive data loss and critical system disruption.
Some of these services that particularly stood out to me include:
- Continuous Diagnostics and Mitigation (CDM) Program – Offered cybersecurity tools like endpoint detection and response (EDR) and security information and event management (SIEM) to agencies at low cost to fit into agency budgets,
- Vulnerability Disclosure Program (VDP) – Established the platform for researchers to report vulnerabilities discovered on agency websites. Through this program, at DOL we were alerted to, and fixed, dozens of issues before they could be exploited.
- Cyber-Hygiene scans and Federal Attack Surface Testing (FAST) – Routine and continuous scanning of agency public-facing assets to detect and report on vulnerabilities, FAST taking a deeper dive than the hygiene scans. Like with the VDP, these scans and testing alerted our team to numerous potential weaknesses to mitigate … significantly hardening our attack surface.
- Known Exploited Vulnerabilities (KEV) – CISA’s keen analysis of the product weaknesses that most needed attention due to their actual use in exploits helped us immensely to focus our limited resources to address the most critical problems.
- Protective DNS (PDNS) – Prevents agency network traffic from reaching Internet destinations that are categorized as malicious.
- Weekly SOC Calls – Provides a regular forum for the federal cybersecurity practitioner community to hear from CISA experts on the latest threats and exchange concerns and ideas. While designed for practitioners, as CISO I made it a priority to listen in whenever I could. Truly one of the most valuable hours I spent each week.
- Threat hunting support – During high-profile events like SolarWinds and Log4j, CISA experts provided invaluable support with intel and advice on indicators of compromise (IOCs), hunting techniques, and cleanup and recovery procedures.
Again, these are merely a subset of what CISA provides. A complete list of the CISA services is available at Services | CISA.
Praise, as well, for the amazing outreach and collaboration from CISA to agencies. From the regular, formal, high-level strategy sessions on topics like cyber metrics, zero trust, post-quantum cryptography (PQC), and AI, to the monthly check-ins with our assigned Agency Cyber Officer to discuss priorities, concerns, and requests. I was honored to have been your colleague in federal service.
Also, a tip of the cap to all the CISA team working for the last two months under a cloud of paycheck uncertainty.
Like many, I don’t know what size or shape CISA will take in the future. But I know CISA should be proud of its past and that it is dedicated to its mission in the present. For all our sakes, I will remain hopeful for its future.
The threat landscape that made CISA necessary hasn’t softened. If anything, attacks against federal networks and critical infrastructure have accelerated. Whatever form CISA takes going forward, the mission it was built to serve remains as urgent as ever.